The LockBit ransomware gang has suffered a knowledge breach after its darkish internet affiliate panels had been defaced and changed with a message linking to a MySQL database dump.
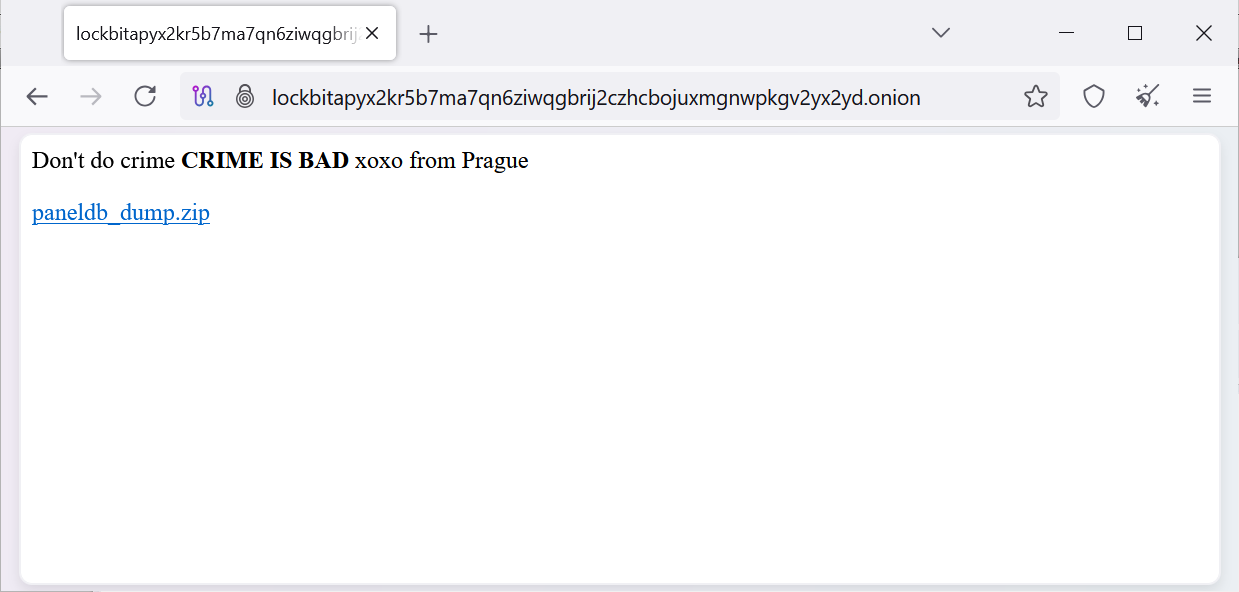
All the ransomware gang’s admin panels now state. “Do not do crime CRIME IS BAD xoxo from Prague,” with a hyperlink to obtain a “paneldb_dump.zip.”
As first noticed by the menace actor, Rey, this archive incorporates a SQL file dumped from the location affiliate panel’s MySQL database.
From evaluation by BleepingComputer, this database incorporates twenty tables, with some extra fascinating than others, together with:
- A ‘btc_addresses‘ desk that incorporates 59,975 distinctive bitcoin addresses.
- A ‘builds‘ desk incorporates the person builds created by associates for assaults. Desk rows comprise the general public keys, however no non-public keys, sadly. The focused firms’ names are additionally listed for a number of the builds.
- A ‘builds_configurations‘ desk incorporates the totally different configurations used for every construct, similar to which ESXi servers to skip or information to encrypt.
- A ‘chats‘ desk may be very fascinating because it incorporates 4,442 negotiation messages between the ransomware operation and victims from December nineteenth to April twenty ninth.
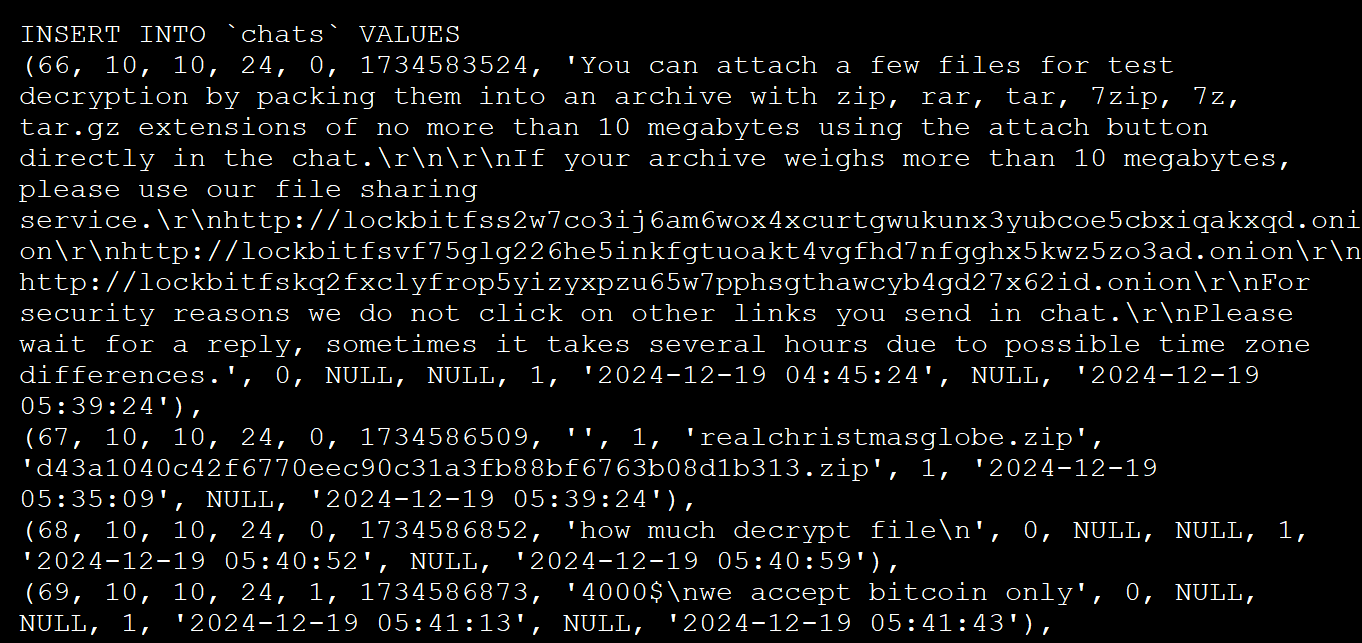
Affiliate panel ‘chats’ desk - A ‘customers‘ desk lists 75 admins and associates who had entry to the affiliate panel, with Michael Gillespie recognizing that passwords had been saved in plaintext. Examples of a number of the plaintext passwords are ‘Weekendlover69, ‘MovingBricks69420’, and ‘Lockbitproud231’.
In a Tox dialog with Rey, the LockBit operator often called ‘LockBitSupp’ confirmed the breach, stating that no non-public keys had been leaked or information misplaced.
Primarily based on the MySQL dump technology time and the final date document within the negotiation chats desk , the database seems to have been dumped in some unspecified time in the future on April twenty ninth, 2025.
It is unclear who carried out the breach and the way it was executed, however the defacement message matches the one utilized in a current breach of Everest ransomware’s darkish site, suggesting a doable hyperlink.
Moreover, the phpMyAdmin SQL dump reveals that the server was operating PHP 8.1.2, which is susceptible to vital and actively exploited vulnerability tracked as CVE-2024-4577 that can be utilized to attain distant code execution on servers.
In 2024, a regulation enforcement operation referred to as Operation Cronos took down LockBit’s infrastructure, together with 34 servers internet hosting the info leak web site and its mirrors, information stolen from the victims, cryptocurrency addresses, 1,000 decryption keys, and the affiliate panel.
Though LockBit managed to rebuild and resume operations after the takedown, this newest breach strikes an additional blow to its already broken status.
It is too early to inform if this extra status hit would be the remaining nail within the coffin for the ransomware gang.
Different ransomware teams who’ve skilled comparable leaks embrace Conti, Black Basta, and Everest.



