Dwelling safety big ADT has confirmed a knowledge breach after the ShinyHunters extortion group threatened to leak stolen information except a ransom is paid.
In a press release shared at this time, the corporate mentioned it detected unauthorized entry to buyer and potential buyer information on April 20, after which it terminated the intrusion and launched an investigation.
This investigation decided that private data was stolen through the breach.
“The investigation confirmed that the knowledge concerned was restricted to names, telephone numbers, and addresses,” ADT advised BleepingComputer.
“In a small share of instances, dates of delivery and the final 4 digits of Social Safety numbers or Tax IDs had been included. Critically, no cost data — together with financial institution accounts or bank cards — was accessed, and buyer safety methods weren’t affected or compromised in any method.”
ADT says the intrusion was restricted and that it has contacted all affected people.
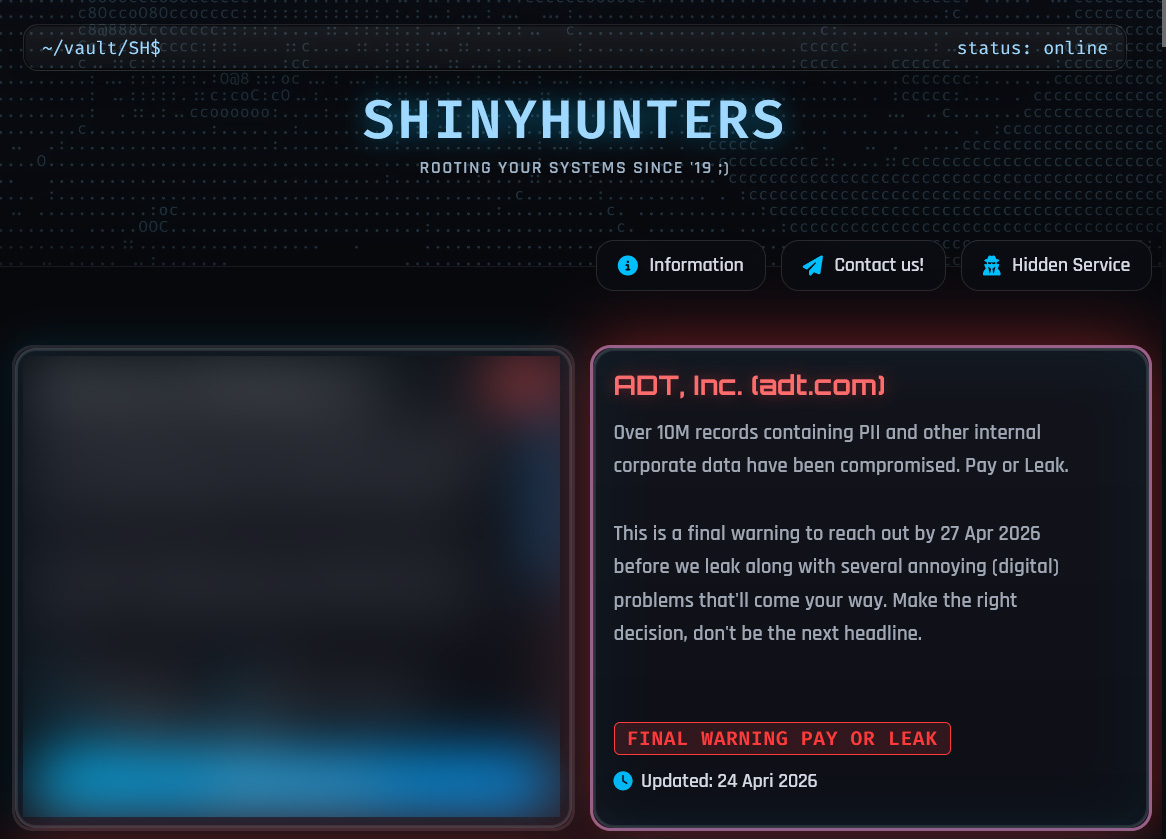
ShinyHunters leak web site itemizing
This assertion follows ADT’s itemizing on the ShinyHunters information leak web site, the place attackers claimed to have stolen 10 million information containing prospects’ private data.
“Over 10M information containing PII and different inner company information have been compromised. Pay or Leak,” reads the information leak web site.
“It is a ultimate warning to achieve out by 27 Apr 2026 earlier than we leak together with a number of annoying (digital) issues that’ll come your method.”
ADT didn’t affirm the amount of information theft claimed by the attackers.
ShinyHunters advised BleepingComputer they allegedly breached ADT by way of a voice phishing (vishing) assault that compromised an worker’s Okta single sign-on (SSO) account. Utilizing this account, the menace actors claimed they accessed and stole information from the corporate’s Salesforce occasion.
Since final 12 months, the extortion group has been conducting widespread vishing campaigns that focus on staff and BPO brokers’ Microsoft Entra, Okta, and Google SSO accounts.
After having access to a company SSO account, the menace actors steal information from linked SaaS functions akin to Salesforce, Microsoft 365, Google Workspace, SAP, Slack, Adobe, Atlassian, Zendesk, Dropbox, and plenty of others.
This stolen information is then used to extort the corporate into paying a ransom, or the information can be leaked.
ADT has beforehand disclosed information breaches in August and October 2024 that uncovered buyer and worker data.
AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Autonomous Validation Summit (Might 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls maintain, and closes the remediation loop.




