The deployment of autonomous AI brokers—techniques able to utilizing instruments and executing code—presents a novel safety problem. Whereas normal LLM purposes are restricted to text-based interactions, autonomous brokers require entry to shell environments, file techniques, and community endpoints to carry out duties. This elevated functionality introduces vital dangers, as a mannequin’s ‘black field’ nature can result in unintended command execution or unauthorized knowledge entry.
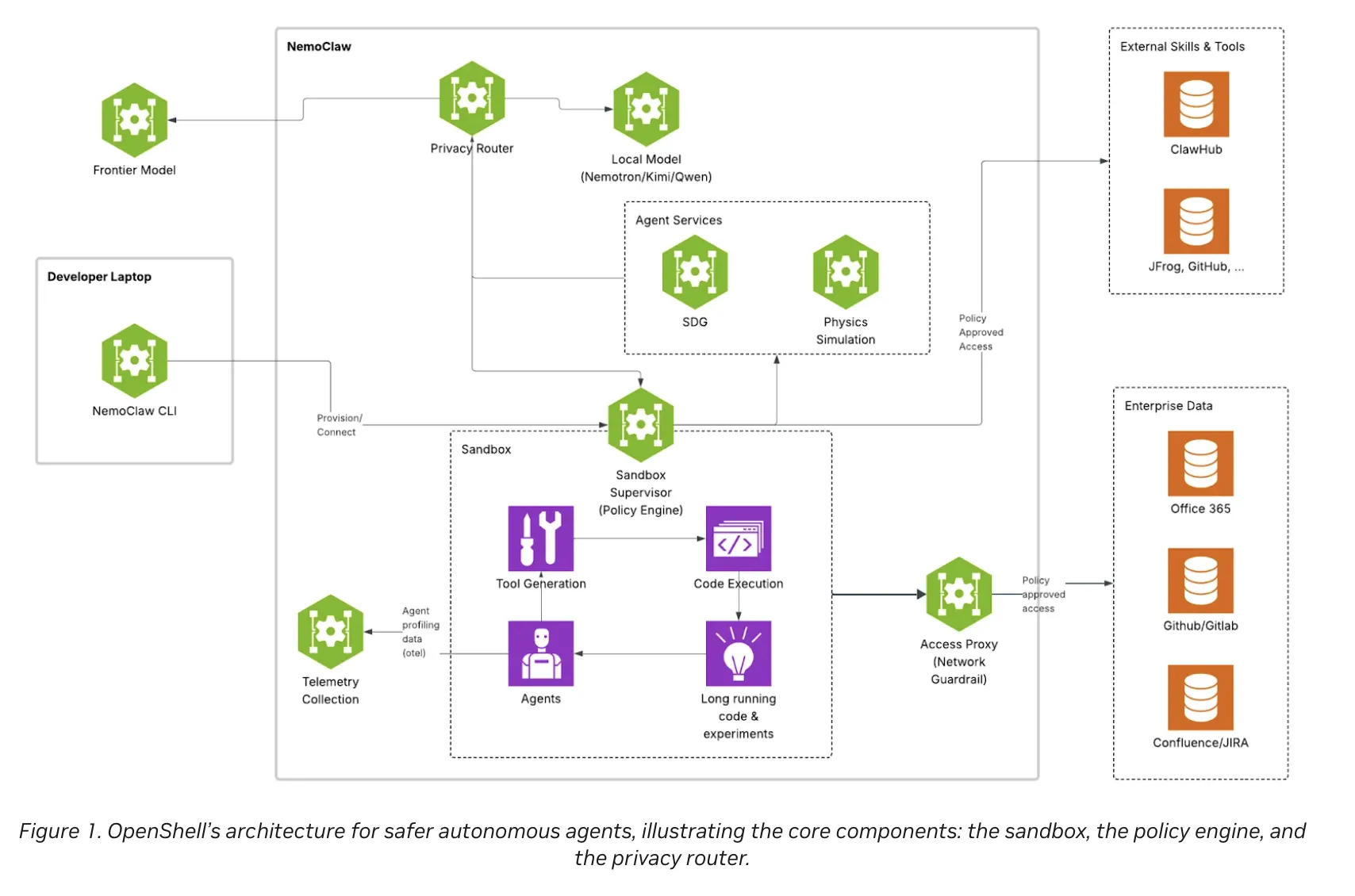
NVIDIA has addressed this hole by open-sourcing OpenShell, a devoted runtime atmosphere designed to facilitate the secure execution of autonomous brokers. Launched below the Apache 2.0 license, OpenShell offers a framework for sandboxing, entry management, and inference administration.
The Structure of Agent Security
OpenShell capabilities as a protecting layer between the AI agent and the working system. For AI devs, this implies the agent’s ‘tool-use’ capabilities are restricted by a predefined safety posture moderately than counting on the mannequin’s inside alignment.
1. Sandboxed Execution
OpenShell makes use of kernel-level isolation to create an ephemeral execution atmosphere. By sandboxing the agent, any code generated—whether or not it’s a Python script or a Bash command—is executed inside a restricted area. This prevents an agent from accessing delicate host recordsdata or modifying system configurations except explicitly permitted.
2. Coverage-Enforced Entry Management
OpenShell’s governance core is its granular coverage engine. Not like conventional container safety, which regularly operates on broad permissions, OpenShell permits for:
- Per-binary management: Limiting which executables (e.g.,
git,curl,python) the agent can invoke. - Per-endpoint management: Limiting community visitors to particular IP addresses or domains.
- Per-method management: Governing particular API calls or shell capabilities.
These insurance policies are ‘explainable,’ that means each motion is logged in an audit log. This offers a transparent path for debugging and compliance, permitting devs to confirm precisely why a selected motion was blocked or permitted.
3. Non-public Inference Routing
OpenShell features a devoted layer for non-public inference routing. This mechanism intercepts mannequin visitors to implement privateness and price constraints. It ensures that delicate knowledge just isn’t leaked to exterior mannequin suppliers and permits organizations to change between native and cloud-based LLMs with out modifying the agent’s core logic.
Agent Agnostic Integration
A key technical benefit of OpenShell is that it’s agent agnostic. It doesn’t require builders to rewrite brokers utilizing a selected SDK or framework. Whether or not a crew is using Claude Code, Codex, OpenClaw, or a customized LangChain-based system, OpenShell acts as a runtime wrapper. This permits for a constant safety layer throughout various agent architectures.
Developer Workflow and CLI
OpenShell is designed for integration into current CI/CD pipelines and native improvement environments. It offers a Command Line Interface (CLI) and a Terminal UI (TUI) for real-time monitoring of agent habits.
Engineers can initialize a sandbox utilizing easy instructions:
# Create a sandbox for a selected agent
openshell sandbox create --
# Enter the sandbox terminal to observe or work together
openshell time period The runtime additionally helps reside coverage updates. If an agent requires further permissions throughout a process, devs can modify the coverage file with out restarting the sandbox, and the adjustments are utilized instantly.
Distant Sandbox Assist
For distributed groups or heavy compute workloads, OpenShell helps distant execution. This permits a developer to handle a sandbox working on a high-performance GPU cluster from a neighborhood terminal:
openshell sandbox create --remote consumer@host -- Abstract of Key Highlights
| Characteristic | Technical Profit |
| Apache 2.0 | Open-source flexibility for enterprise and private use. |
| Landlock LSM | Kernel-level isolation for sturdy sandboxing. |
| L7 Coverage Enforcement | Granular management over community and binary execution. |
| Audit Logging | Full transparency for agent actions and decision-making. |
| Non-public Routing | Price and privateness controls for LLM inference visitors. |
OpenShell is a foundational device for anybody constructing autonomous agent techniques that require real-world device entry. By standardizing the runtime, NVIDIA helps the trade transfer previous experimental scripts towards safe, ruled autonomous brokers.
Try Codes, Docs and Technical particulars. Additionally, be at liberty to comply with us on Twitter and don’t neglect to affix our 120k+ ML SubReddit and Subscribe to our Publication. Wait! are you on telegram? now you’ll be able to be a part of us on telegram as effectively.


